Due to pressure of local regulatory compliance issues and/or corporate governance demands there is a growing awareness of Governance Risk and Compliance among executive management. This blog describes how to get in control of the SAP system using CSI tooling.
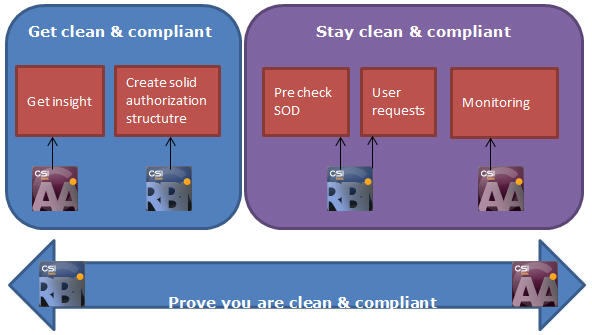
1. Get clean and compliant
First, get insight in the status of the current access governance. CSI Authorization Auditor© (CSI AA) helps getting insight in a fast and easy way of the current access governance. Who can access which data and did they execute it? Who has broad access through different stages of the process and therefore segregation of duty conflicts and did they execute all activities within the conflict? Are all the backdoors secured? Are there inconsistencies in roles, user role assignments or in the rule set? CSI Authorization Auditor gives the answer using a multi layered analysis.
Once the insight is there, it might be necessary to make changes in the current set up of the security concept to get a solid access governance. This is fully supported by CSI Role Build & Manage© (CSI RBM) with features like automatic role building and deriving of roles (using reverse engineering), consistency checks and pre SOD check of the roles. CSI RBM speeds up the phase to get clean & compliant. Monitor if the concept is improving with Dashboards in CSI Authorization Auditor.
2. Stay clean and compliant
Once the access governance is clean and compliant the next step will be “stay clean & compliant”; Define the Business processes, risks and controls on the fly. Monitor the security concept and store the evidence in CSI Authorization Auditor 2014. Stay compliant with your clean security concept using RBM’s user request functionality with pre SOD checking for the authorization and user changes.
3. Prove you are complaint
Monitor the risks and controls and document all the evidence in CSI Authorization Auditor 2014 to prove you are compliant. The audit committee can use CSI Authorizaiton Auditor stand alone with their rule set to check the authorization structure independently. Changed to the rule set in CSI Authorizaiton Auditor 2014 and roles in CSI RBM are logged automatically.
Advantages CSI tooling:
• CSI Authorization Auditor 2014 covers all aspects of access governance
• Use CSI Authorization Auditor to monitor small systems that are not in scope for SAP GRC
• The audit committee can use CSI Autorization Auditor PC based. Only they have access to the audit rule set and perform independent audits.
• Documenting the security process can take a long time. CSI Authorization Auditor 2014 can simultaneous implement and document the business process with risks and controls step by step. Add any information about the security process to CSI Authorization Auditor 2014 and make changes on the fly. Use CSI Authorization Auditor 2014 to document the security process in a fast way.
• Fast implementation time, have the first results within a week (depending on the system)
• Clear overview of SOD conflicts and how to solve them, results are on different views expandable.
• A sequence of dialog boxes leads the user through a series of well-defined steps (wizard). Tasks that are infrequently performed are easier to perform using the wizard. CSI Authorization Auditor 2014 supports reporting the right results in the fastest way. Because of the use of the new interface and wizards, users are guided through the application with additional information on the screen, this reduced training effort enormously.
• Messages can be distributed according the RASCI matrix. Implement the organizations’ responsibility assignment matrix to automate the security task messages. People are informed automatically when they need to perform a task in the security process.
• Work simultaneous with multiple users on the same data to see the results in a clear overview, no more manual report distribution.
• CSI Authorization Auditor 2014 comes with a large number of useful reports and dashboards. Is the report or dashboard not fitting the business requirements? Customizing is also possible so create new ones. End-users can define their own grouping of all data shown on screen and every view can be exported to different formats like xlsx, xml, pdf and accdb.
• CSI Authorization Auditor 2014 uses two databases; an application database and an archive database. All original SAP data is saved in the archive as well as all the audit results. The advantages are enormous. Previous audit result are immediately available if needed, the audit results can be compared in detail with previous audit results and new audit roles and requirements can be checked against old downloads. Trending dashboards that show the evolution over period(s) can be produced within seconds.
• New reports and dashboards make it possible to compare the audit results over periods. See if the security concept is improving.
• Analyze the correctness of role assignments with the use of role information and statistical data from the SAP system. CSI Authorization Auditor 2014 also gives a clear view if access rights are accumulating in the security concept. This information can be used to clean up the authorization concept to get in compliance.
• All analyses are done separately on authorization level and transaction code level including executed information. The differences between these results give authorization managers an immediate insight of inconsistencies in the SAP roles and/or audit rules and/or in the access governance process.
• All audit reports have the full causing information available within insight how these access rights are assigned to users. On every level an indication is given if the user needs the role.
• Useful user information can now be found in CSI Authorization Auditor 2014. Always wanted to know which roles are assigned to the user, which transactions a user can (and did) execute (even if the transactions are already removed) and which authorizations is assigned to the user in his user buffer? All this, and more, information is available.
• CSI Authorization Auditor 2014 gives a clear overview about the usage of SAP licenses. Reduce expensive license costs and pay only for the licenses and authorizations that are really being used.
• CSI Authorization Auditor 2014 logs all changes made to the rule sets.
